What Is The Maximum Size Of A Udp User Datagram?
UDP Protocol
In computer networking, the UDP stands for User Datagram Protocol. The David P. Reed developed the UDP protocol in 1980. It is defined in RFC 768, and it is a part of the TCP/IP protocol, so it is a standard protocol over the internet. The UDP protocol allows the computer applications to send the messages in the grade of datagrams from one machine to another machine over the Internet Protocol (IP) network. The UDP is an culling communication protocol to the TCP protocol (manual control protocol). Similar TCP, UDP provides a set up of rules that governs how the data should be exchanged over the net. The UDP works by encapsulating the data into the bundle and providing its own header data to the packet. Then, this UDP packet is encapsulated to the IP packet and sent off to its destination. Both the TCP and UDP protocols transport the information over the internet protocol network, so it is also known as TCP/IP and UDP/IP. There are many differences between these two protocols. UDP enables the process to process communication, whereas the TCP provides host to host advice. Since UDP sends the messages in the form of datagrams, it is considered the best-effort style of communication. TCP sends the individual packets, so information technology is a reliable send medium. Another difference is that the TCP is a connection-oriented protocol whereas, the UDP is a connectionless protocol as it does not require whatsoever virtual circuit to transfer the data.
UDP likewise provides a different port number to distinguish dissimilar user requests and also provides the checksum capability to verify whether the complete data has arrived or not; the IP layer does not provide these two services.
Features of UDP protocol
The following are the features of the UDP protocol:
- Ship layer protocol
UDP is the simplest ship layer advice protocol. It contains a minimum amount of communication mechanisms. It is considered an unreliable protocol, and it is based on all-time-effort delivery services. UDP provides no acknowledgment machinery, which means that the receiver does not send the acquittance for the received packet, and the sender as well does not wait for the acknowledgment for the parcel that information technology has sent.
- Connectionless
The UDP is a connectionless protocol as it does not create a virtual path to transfer the data. Information technology does not use the virtual path, so packets are sent in different paths between the sender and the receiver, which leads to the loss of packets or received out of order.
Ordered commitment of data is not guaranteed.
In the case of UDP, the datagrams are sent in some society will be received in the same order is not guaranteed as the datagrams are not numbered.
- Ports
The UDP protocol uses different port numbers and then that the data can be sent to the right destination. The port numbers are defined betwixt 0 and 1023.
- Faster transmission
UDP enables faster manual as information technology is a connectionless protocol, i.due east., no virtual path is required to transfer the information. But there is a chance that the private bundle is lost, which affects the transmission quality. On the other hand, if the parcel is lost in TCP connection, that packet will be resent, so it guarantees the delivery of the data packets.
- Acquittance mechanism
The UDP does have any acknowledgment machinery, i.eastward., in that location is no handshaking between the UDP sender and UDP receiver. If the message is sent in TCP, so the receiver acknowledges that I am ready, and then the sender sends the data. In the case of TCP, the handshaking occurs between the sender and the receiver, whereas in UDP, there is no handshaking between the sender and the receiver.
- Segments are handled independently.
Each UDP segment is handled individually of others every bit each segment takes different path to attain the destination. The UDP segments can be lost or delivered out of order to reach the destination as there is no connection setup betwixt the sender and the receiver.
- Stateless
It is a stateless protocol that ways that the sender does not become the acknowledgement for the package which has been sent.
Why practise we crave the UDP protocol?
As we know that the UDP is an unreliable protocol, but nosotros still require a UDP protocol in some cases. The UDP is deployed where the packets require a large amount of bandwidth forth with the actual information. For example, in video streaming, acknowledging thousands of packets is troublesome and wastes a lot of bandwidth. In the case of video streaming, the loss of some packets couldn't create a problem, and it can likewise be ignored.
UDP Header Format
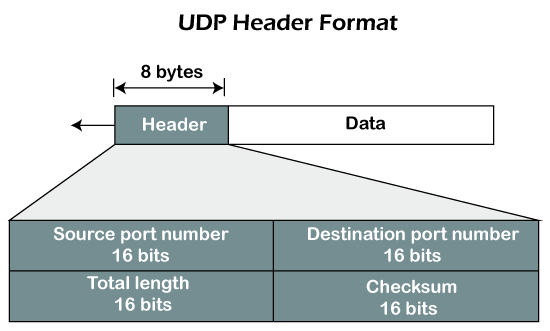
In UDP, the header size is 8 bytes, and the package size is upto 65,535 bytes. But this packet size is not possible as the data needs to be encapsulated in the IP datagram, and an IP packet, the header size can be 20 bytes; therefore, the maximum of UDP would be 65,535 minus 20. The size of the data that the UDP packet tin can acquit would be 65,535 minus 28 as eight bytes for the header of the UDP packet and 20 bytes for IP header.
The UDP header contains iv fields:
- Source port number: Information technology is 16-chip data that identifies which port is going t send the packet.
- Destination port number: It identifies which port is going to accept the information. It is 16-bit information which is used to identify application-level service on the destination machine.
- Length: It is 16-flake field that specifies the entire length of the UDP bundle that includes the header also. The minimum value would be 8-byte equally the size of the header is 8 bytes.
- Checksum: Information technology is a 16-bits field, and it is an optional field. This checksum field checks whether the data is accurate or not as there is the possibility that the information tin can exist corrupted while transmission. It is an optional field, which means that it depends upon the application, whether it wants to write the checksum or not. If it does not want to write the checksum, then all the 16 bits are zippo; otherwise, it writes the checksum. In UDP, the checksum field is applied to the unabridged parcel, i.due east., header likewise as data part whereas, in IP, the checksum field is applied to simply the header field.
Concept of Queuing in UDP protocol
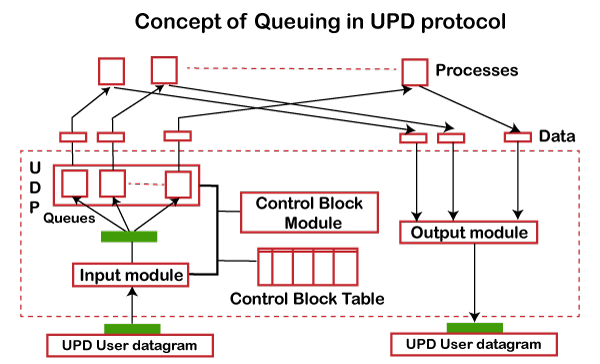
In UDP protocol, numbers are used to distinguish the different processes on a server and customer. We know that UDP provides a procedure to process advice. The customer generates the processes that demand services while the server generates the processes that provide services. The queues are available for both the processes, i.e., two queues for each process. The starting time queue is the incoming queue that receives the letters, and the second one is the outgoing queue that sends the messages. The queue functions when the process is running. If the process is terminated and so the queue will also get destroyed.
UDP handles the sending and receiving of the UDP packets with the help of the following components:
- Input queue: The UDP packets uses a set of queues for each process.
- Input module: This module takes the user datagram from the IP, and so it finds the data from the control block table of the same port. If it finds the entry in the control block table with the same port every bit the user datagram, information technology enqueues the data.
- Control Cake Module: It manages the control block table.
- Control Cake Table: The control block table contains the entry of open up ports.
- Output module: The output module creates and sends the user datagram.
Several processes want to use the services of UDP. The UDP multiplexes and demultiplexes the processes so that the multiple processes tin can run on a unmarried host.
Limitations
- It provides an unreliable connexion delivery service. It does not provide any services of IP except that it provides procedure-to-procedure advice.
- The UDP message can be lost, delayed, duplicated, or can be out of order.
- It does not provide a reliable transport commitment service. It does not provide any acknowledgment or menstruation command mechanism. Nevertheless, it does provide error control to some extent.
Advantages
- Information technology produces a minimal number of overheads.
What Is The Maximum Size Of A Udp User Datagram?,
Source: https://www.javatpoint.com/udp-protocol
Posted by: williamscrou1946.blogspot.com


0 Response to "What Is The Maximum Size Of A Udp User Datagram?"
Post a Comment